YouTube Launches PayPal Stablecoin Payments for US Creators
We independently review everything we recommend. When you buy through our links, we may earn a commission which is paid directly to our Australia-based writers, editors, and support staff. Thank you for your support!

Brief Overview
- YouTube collaborates with PayPal to enable stablecoin payouts in PYUSD for creators in the US.
- PayPal’s stablecoin, PYUSD, is supported by US dollar deposits.
- This initiative seeks to facilitate quicker, more affordable transactions for creators.
- Initially available only in the US, with possibilities for worldwide reach.
- Australian creators might gain from improved currency conversion rates.
Launch of Stablecoin Payouts by YouTube and PayPal
YouTube has made a notable advancement in evolving the payment methods for content creators by partnering with PayPal to roll out stablecoin payouts. Creators in the YouTube Partner Program in the US can now receive their earnings in PayPal USD (PYUSD), a shift that may revolutionise the economic landscape for digital creators on a global scale.
Decoding PayPal’s Stablecoin: PYUSD
Introduced in 2023, PYUSD is PayPal’s own stablecoin, completely backed by US dollar deposits and cash equivalents, ensuring dependability and stability. Unlike fluctuating cryptocurrencies like Bitcoin or Ethereum, PYUSD provides a stable digital substitute for the US dollar, allowing seamless transactions online with the benefits of blockchain technology.
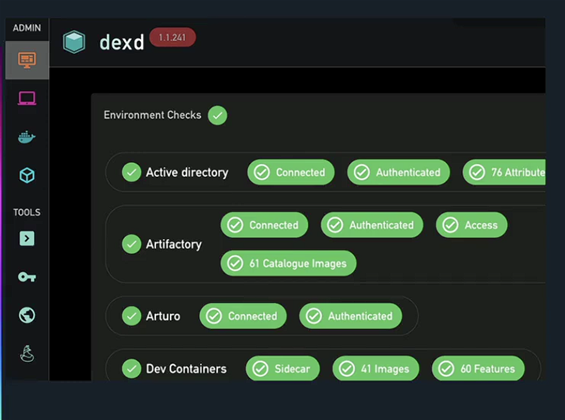
Understanding the Integration Process
YouTube’s collaboration with PayPal leverages established payout frameworks, allowing YouTube to issue payments in conventional US Dollars. PayPal then converts these funds to PYUSD for creators who choose to participate, streamlining processes while capitalising on the advantages of blockchain settlements.
Benefits for Creators
The main advantages for creators involve efficiency and reduced costs. Conventional international wire transfers tend to be sluggish and costly. In contrast, blockchain transactions can be completed swiftly, significantly lowering intermediary fees. May Zabaneh, PayPal’s Head of Crypto, highlighted the rapid settlements and decreased fees this system provides, tackling prevalent challenges encountered by digital professionals.
Consequences for Australian Creators
While presently restricted to the US, the impact on Australian creators is considerable. A significant obstacle for local YouTubers is the friction in currency conversion. Payments made in USD typically yield unfavorable exchange rates and substantial transaction costs when transformed to AUD. A global expansion of this initiative could enable Australian creators to retain earnings in USD or convert them more effectively, circumventing traditional banking difficulties.
Expanding Market and Blockchain Features
Since its inception, PYUSD has reached a market capitalization of nearly A$6 billion, functioning on both Ethereum and Solana blockchains. The latter provides enhanced speed and lower costs for transactions, making PYUSD more attractive for international dealings.
Final Thoughts
The partnership between YouTube and PayPal enhances an existing collaboration with Google’s AdSense platform, showcasing a tangible application of Web3 technologies. By incorporating stablecoins like PYUSD, YouTube endorses the use of digital assets in mainstream financial exchanges, suggesting a change in how leading tech companies view global payments.
Recap
YouTube’s partnership with PayPal to provide stablecoin payouts represents a major evolution in payment methods for content creators. With the launch of PayPal’s PYUSD stablecoin, creators enjoy faster and more cost-efficient transactions. While it is currently available only in the US, potential global expansion could significantly aid Australian creators by enhancing currency conversion processes and lowering banking costs.