In Images: Protecting AI Agents and NHIs – Perspectives from Saviynt Melbourne Roundtable
We independently review everything we recommend. When you buy through our links, we may earn a commission which is paid directly to our Australia-based writers, editors, and support staff. Thank you for your support!
AI Agents and Non-Human Identities: Insights from Melbourne

Brief Overview
- AI and NHIs are becoming increasingly crucial to business functions.
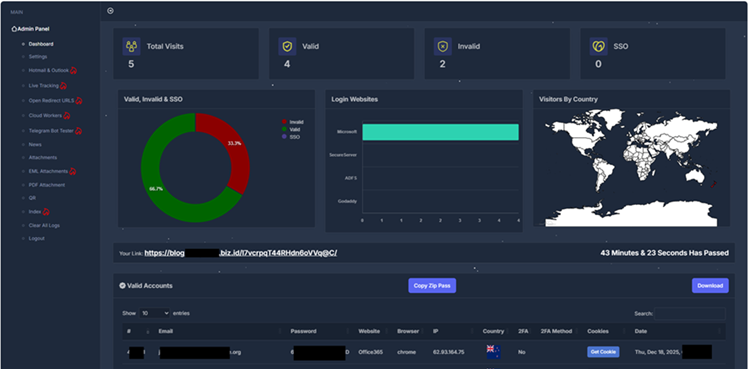
- Cybersecurity risks targeting AI frameworks are advancing quickly.
- Strong governance structures are critical for AI protection.
- Partnership among industry experts is essential for tackling AI issues.
Defining AI and Non-Human Identities
Artificial Intelligence (AI) and Non-Human Identities (NHIs) are reshaping the operational landscape for businesses throughout Australia. As these innovations become more integral to daily functions, it is vital to secure them against cyber threats.
Cybersecurity Obstacles
The swift advancement of AI technologies has introduced fresh cybersecurity challenges. Given that AI agents can function independently, they may be at risk of manipulation or exploitation by hostile entities. Thus, the implementation of strong security protocols is crucial to defend against possible breaches.
Governance and Structures
Developing sound governance structures is necessary to maintain the safety and integrity of AI technologies. Such frameworks assist in risk management and regulatory compliance, thereby enhancing trust in AI offerings.
Collaborative Efforts in the Industry
The Saviynt Melbourne Roundtable underscored the necessity of cooperation among industry players to confront the difficulties linked with AI and NHIs. By exchanging knowledge and strategies, industry leaders can more effectively navigate the intricacies of AI deployment and security.
Conclusion
The Saviynt Melbourne Roundtable brought to light the vital requirement for comprehensive security measures and collaborative initiatives in protecting AI agents and NHIs. As AI innovations become progressively essential, it is crucial to tackle cybersecurity issues through effective governance and industry collaboration for the benefit of Australian enterprises.