Meta Broadens Smart Eyewear Collection with New Prescription-Ready Ray-Ban and Oakley Styles
We independently review everything we recommend. When you buy through our links, we may earn a commission which is paid directly to our Australia-based writers, editors, and support staff. Thank you for your support!
Quick Read
- Meta and EssilorLuxottica enhance smart eyewear with fresh Ray-Ban and Oakley designs.
- New models like Blayzer and Scriber emphasize comfort and compatibility with prescriptions.
- Oakley collection upgraded with Prizm and Transitions lenses suited for various settings.
- Glasses now provide real-time translation in 20 additional languages.
- Available in Australia from 15 April, priced from A$709.
Addressing the Need for Daily Use
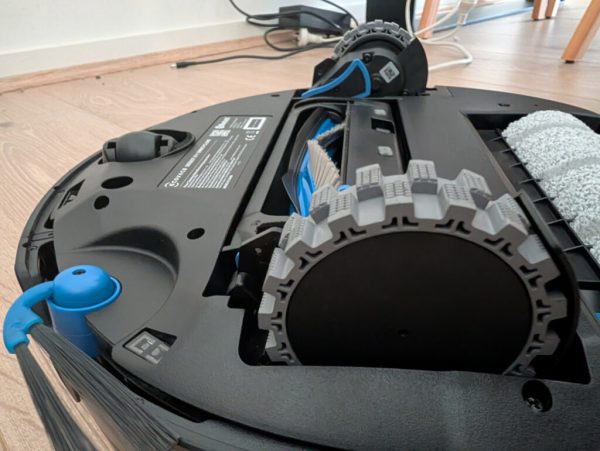
The fresh Ray-Ban Meta Optics Styles unveil the Blayzer and Scriber frames, both crafted for comfort throughout the day and designed to work with prescription lenses. The Blayzer features a timeless rectangular design, while the Scriber offers a rounded aesthetic, appealing to a variety of style preferences.
Meta has focused on ergonomics with elements like overextension hinges, replaceable nose pads, and adjustability in temple tips by opticians, ensuring a customized fit for every user.
New Colours and Oakley Expansion
Alongside classic black frames, seasonal colours like Transparent Dark Olive and Matte Transparent Peach enhance the range. For active enthusiasts, Oakley’s Vanguard and HSTN models now offer a wider selection of Prizm and Transitions lenses, optimized for various activities.
The addition of Prizm Dark Golf lenses boosts functionality, allowing users to engage in sports like golf with better visual contrast while remaining connected via the AI assistant.
Eliminating Language Barriers
The software of the glasses receives a major update, now capable of translating speech in real-time across 20 new languages, including Mandarin and Arabic. This makes the eyewear a valuable asset for international travel, facilitating smooth communication without relying on a smartphone.
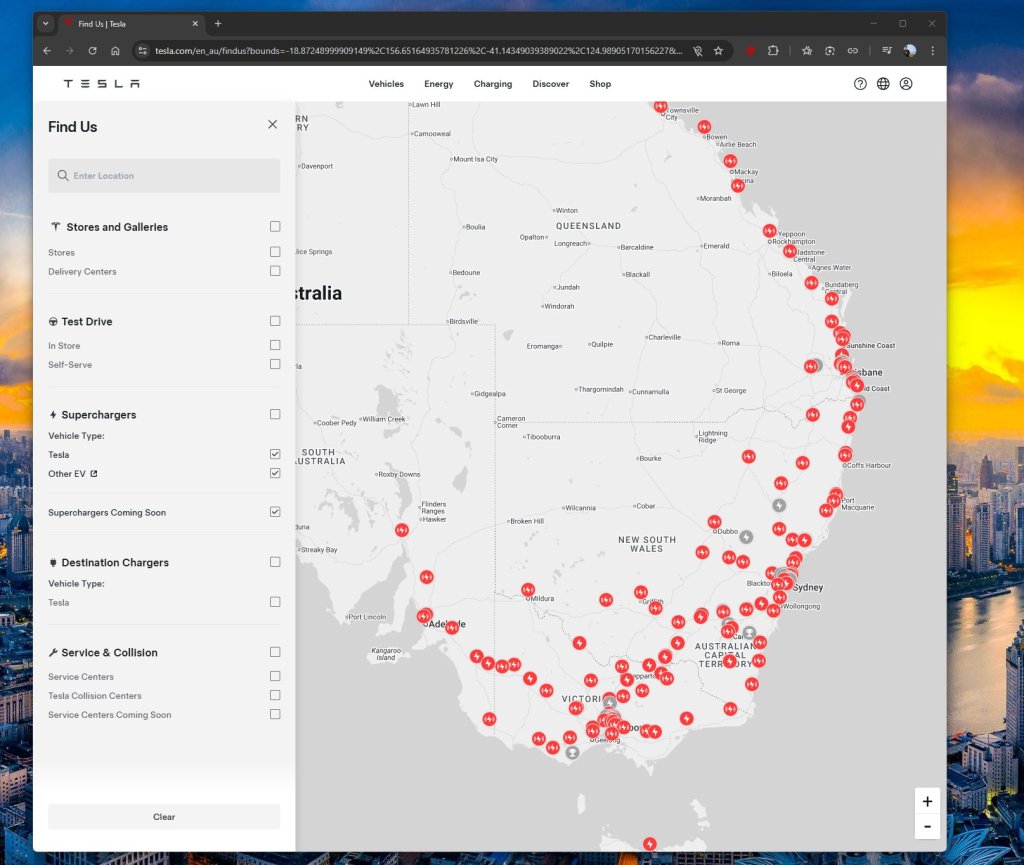
Meta is also broadening its retail footprint into regions like Japan, Korea, and Singapore, indicating strong confidence in the global market for smart eyewear.
Pricing and Availability in Australia
In Australia, the new Ray-Ban Meta Optics Styles will launch from select optical retailers on 15 April, starting at A$709. The Oakley collection will follow with staggered introductions in May, featuring new Prizm Transitions options.
A New Chapter for the Vision Impaired
With the integration of prescription support, Meta’s smart glasses evolve from a niche gadget to a mainstream eyewear choice. Their similarity to conventional high-end Ray-Bans is a notable benefit, delivering advanced features such as live translation and discreet photo capture.
Concluding Thoughts
If you’ve been anticipating the evolution of smart glasses into a functional daily accessory, this new launch might be your signal. With enhanced comfort, a broader array of style choices, and advanced lens technology, these glasses offer an enticing fusion of style and practicality. Stay tuned for an in-depth review once we get firsthand experience with them in Australia.
Summary
Meta’s latest enhancements to its smart eyewear collection, showcasing new Ray-Ban and Oakley styles, signify a substantial progression in wearable technology. With better comfort, diverse styles, and useful features like real-time translation, these glasses present an appealing option for tech-savvy eyewear users.